In today’s digital age, businesses are rapidly transitioning to cloud infrastructures to leverage scalability, flexibility, and cost-effectiveness. However, with this transition comes a myriad of security challenges, challenges that can be overcome with proper planning and an understanding of potential pitfalls. Based on the Cloud Security Maturity Model (CSMM), a comprehensive framework for assessing, enhancing, and monitoring the security posture of cloud services, Check Point assessment service will help you build a robust transformation plan for your cloud security program
Benefits
Our assessment and advisory services offers clients a realistic and pragmatic approach to cloud transofmraion supported by a cros functional team of industry experts and backed by the Cloud Security Maturity Model (CSMM). Our vendor agnostic service applies a a structured framework-based process to assess, improve, and maintain your cloud security posture. The service delivers:
- Security Assessment and Gap Analysis: Evaluating the current cloud security posture and identifying gaps compared to industry benchmarks and best practices.
- Risk Assessment and Prioritization: Identifying and prioritizing risks to focus on mitigating the most critical vulnerabilities.
- Compliance Review and Advisory: Ensuring alignment with relevant regulatory requirements and industry standards to avoid compliance issues.
- Strategic Security Roadmap Development: Creating a strategic and actionable roadmap for improving cloud security maturity over time.
- Customized Security Recommendations: Providing tailored advice and recommendations based on the organization’s unique business context and needs.
- CNAPP and Cloud Security Architecture: Creating target high level Cloud Security Architecture blueprint based on the CNAPP model and relevant cloud security native technologies.
- Continuous Monitoring and Improvement Framework: Establishing a system for ongoing assessment and enhancement of cloud security measures.
Delivery
The Check Point team prepares for success with in-depth engagement planning up to six weeks before our onsite time. With a firm plan, we’ll spend one day onsite, working with you on the following activities:
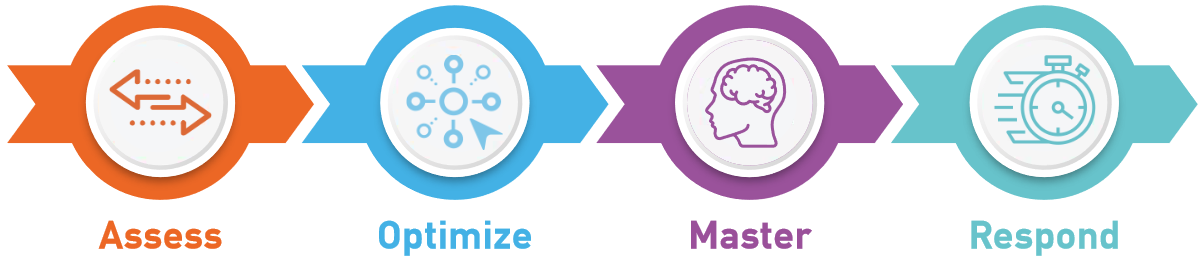
- Deploy: Leverage Check Point technology platforms to collect data on your cloud security configuration, allowing real world configuration data to be included in the assessment dataset, alongside this the assessment team will define the client teams ownership of assessment controls
- Collect: interview and workshop sessions for data collection and interview, where necessary controls are evidenced, on average the process is completed within 2-5 working days
- Analysis: Check Point Architecture team from Risk, compliance and cloud teams analysis data collected manually and though our technology and define risk register and maturity level
- Reporting: document preparation including a comprehensive document outlining the current state of cloud security, including identified vulnerabilities, gaps, and risks.
- Risk Assessment Matrix: A detailed matrix categorizing and prioritizing identified risks based on their potential impact and likelihood.
- Compliance Assessment Document: A report detailing the organization’s compliance status with relevant regulations and standards and any gaps.
- Cloud Security Roadmap: A strategic document outlining a step-by-step plan for improving cloud security maturity, including short-term and long-term initiatives.
- High Level Target Cloud security design: cloud security architecture blueprint and CNAPP implementation plan
- Recommendation Action Plan: A list of customized recommendations and best practices tailored to the organization’s specific context, with actionable steps for implementation.
- Continuous Improvement Plan: A framework or guideline for ongoing monitoring, assessment, and enhancement of cloud security practices, including metrics and KPIs for measurement.

Most relevant roles
CISO, CIO, Compliance Officer, Risk Manager, Cloud Architect, Cloud Security Consultant/Advisor, Security Architects

Ideal number of participants
2-5 Professionals
Infinity Global Services
Check Point Infinity Global Services provides end-to-end security services that enables you to grow your team’s expertise, design best practices and prevent threats in real time. Wherever you are in your cybersecurity journey, we start there. Our elite experts will work together with your team to take your organization to the next level of protection and build your cyber resilience plan.